Table of Contents
Introduction
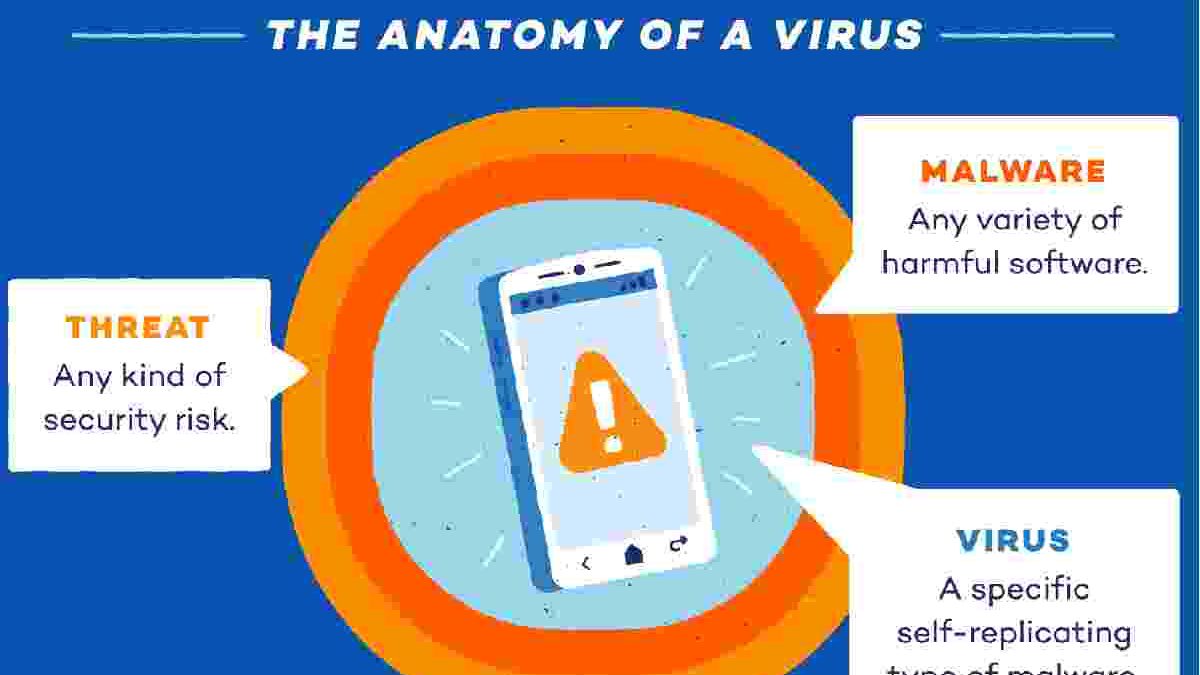
Protecting your data is very important to ensure that it is not accessed by third parties that you may use wrongly. Smartphones have a lot of vulnerabilities to viruses and malware but remain safer than computers.
Computers have swept our lives with all their joints and are almost everywhere; they are used in the media, government departments, education systems and many other areas of life. At first, big companies used full-room computers, but with great sophistication. This size has shrunk to fit our pockets!
This development also carries excellent risks. Some parties can plant malicious software that leads to chaos and problems for the user, primarily since most people rely on automating their tasks digitally from the most accurate to the most. The emergence of this malware coincided with the advent of personal computers, but are smartphones safe from these viruses?
do smartphones get infected with viruses? – planting malicious software leads to chaos and problems for the user – security vulnerabilities in operating systems – android platform – android system
What Is A Computer Virus?
The name of the computer virus derives from parasitic viruses found in nature because it resembles natural viruses in their characteristics; it copies itself or modifies specific software in the victim’s device. Viruses arise from reverse engineering security vulnerabilities in operating systems and then tricking a person into installing them.
The extent of damage viruses can cause to the victim’s device varies from mild to severe and catastrophic damage; it may make a key on the keyboard workable, which is frustrating but does not result in the loss of important information. On the other hand, Viruses can cause very significant damage. Such as preventing new applications from being installed, preventing existing applications from working, or deleting user data entirely, including backups and hard drives, and can hack into all personal financial information.
Historically, viruses have been the first target by windows due to their widespread. Recently, Apple has faced similar challenges. Hackers continue to devise new ways to penetrate operating systems, causing severe financial damage and losses to both individuals and companies.
How Do Viruses Affect Computers?
With the tremendous scientific development and modernization of protection systems, it has become difficult for hackers or hackers to exploit and manipulate vulnerabilities in operating systems. The only obstacle to them is to install viruses on the victim’s device. So they work cunningly and in innovative ways to deceive the recipient. Such as sending an email containing a link to win a valuable prize or downloading a link for a free program that the user was looking for or maybe an addition to a known and secure program and when pressed on these links hackers can penetrate the operating system. And access to information.
After installing viruses on the victim’s device that works like RAT: Remote Access Tools, which provide access to all system functions. This seems disastrous as it allows them to access all the user’s personal information and data, access the user’s camera, photograph the surrounding environment, and then blackmail him for money or sell this information in different places.
As it later became clear, smartphones are not affected by traditional viruses that infect computers. Still, some viruses can damage the mobile phone’s operating system. And there are multiple ways to penetrate it.
How Do Viruses Affect Smartphones?
Installing apps on a mobile phone is safer than installing them on your computer because the android platform (google play store). And apple’s app store scan apps before allowing them to be published and require all software developers to follow basic guidelines for the safety of use. Which distinguishes smartphones and makes them safe for computers.
Compared to android and apple, android appears to be weaker in protection because it’s an open-source system that allows anyone to access the source code or source code. And identify a potential malicious attack point. Still, Apple doesn’t let anyone know its source code.
Unlike apple, android allows the user to install apps from unknown destinations outside the google store. Although it’s not a default setting, the user can change it, opening the door to malicious applications and software that may reach all user data.
Currently, the standard method of hacking computers is to hack smartphones, namely. To send links containing malicious software that opens a communication channel between the hacker and the victim. Through this connection. The hacker can find a way to hack the device. And downloading content from the internet is also a cause of virus infection of phones.
Tips To Keep Your Phone Safe
Phones have become an integral part of our lives, and through them, they make a lot of money transfers and private and confidential data storage. So it’s essential to keep your phone safe enough from any attempt to hack or sabotage.
first of all, apps from unknown entities don’t prove. And if you have to, look at the app developer. Look for similar programs that they’ve created and check that they’re suspicious or in doubt. And if you’re using android.
Don’t open suspicious messages or links because they can carry a high risk to your device. Don’t carry content from unsafe websites. And only browse known and secure sites. In addition, don’t connect your mobile phone to other dangerous devices that may transmit malicious software to you. And make sure you install antivirus software as well!