Table of Contents
Introduction
The Semantic threat data network collects remote data from millions of attack sensors to detect potential threats before they occur. As well as identify potentially suspicious files. And websites so that information security organizations can take action before they can harm.
Cyberattacks are experiencing increasing complexities in terms of evolution day by day. With new malware variants appearing almost daily. While the number of attacks on the Internet is rising by 56%.
The list includes a range of new practices, such as formjacking. Encryption and the Internet of Things (IoT) attacks within pre-known software such as ransomware and cyber phishing. So it comes when robust protection tools are urgently needed to help counter these continuous waves.
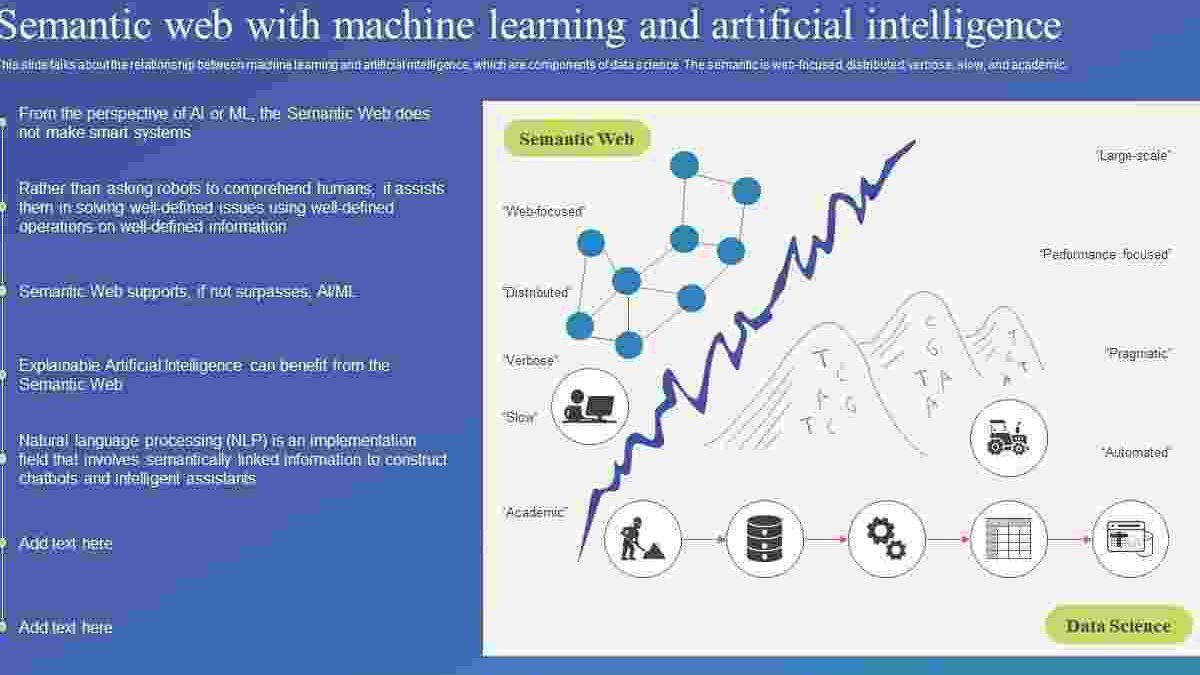
Many believe that cybersecurity plays an essential role in machine learning and ARTIFICIAL INTELLIGENCE capabilities in modern-day tools and platforms. Machine learning methods can help organize and analyze the vast amounts of data collected to activate the threat detection process in real-time.
Industry experts such as PwC expect many organizations to get ai technology and machine learning through cybersecurity use cases. Including identifying distributed service cutting patterns (DDOS) prioritizing usage alerts for gradual handling. An examination of the problem. And risk-based documentation.
According to the PwC’s Global Information Security Status Survey 2018, 27% of organizations plan to invest in cybersecurity defence systems that include some form of artificial intelligence. And machine learning.
For many, cybersecurity plays an essential role in machine learning. And artificial intelligence capabilities. Capabilities included in modern-day tools and platforms.
“Machine learning is one of the best tools for dealing with information security. If you develop a reliable way. You’ll be able to identify patterns that can be used to design specific protection strategies.”
Revealing Patterns
Through the security landscape. Suppliers are aware that machine learning, artificial intelligence. And anything that emerges from this is tools that contribute to changing the security protection in organizations.
Most of the leading security platforms now have machine learning and artificial intelligence capabilities to help detect suspicious movements, help explore new ones. And evolving threats before damaging networks. And facilitate identity verification and documentation.
For example, in the case of Endpoint Protection, advanced machine learning. And artificial intelligence (AI) capabilities work alongside the Global Information Collection Network (GIN).
“Cyberattacks have become very sophisticated. The attackers have become quieter and more accurate, so they have caused more damage,” said Elyse canal, technical director of the art data science team of the crt division of the Carnegie Mellon university institute of software engineering.
Any large-scale organization with 5,000 or more employees will see tens of thousands, if not hundreds of thousands, of accident tickets created monthly or daily. The chance of one person finding two linked tickets is virtually non-existent. Machine learning will find those patterns. “
The ability to predict the exact actions that an attacker may take as part of the intrusion prevention system, for example, may allow proactive measures to be taken to prevent an attack in the first place.
Kunal added that the software engineering institute team would research ways to apply natural language technology to feed computers to find evidence within specification documents to cybersecurity vulnerabilities without the help of analysts.
Semantic Researchers
Semantic researchers also go beyond merely detecting harmful activity but aim to predict the specific steps an opponent may take when carrying out an attack. Unlike other research initiatives that have come to a double conclusion — whether an attack occurs or not — the Semantic report, called Tiresias, expands the run’s capabilities to predict future Clients based on previous observations.
Shin explains the ability to predict the exact actions that an attacker may take as part of the intrusion prevention system. For example, will allow proactive measures to be taken to prevent an attack in the first place.
Of course, there is another aspect to any advantages that artificial intelligence and machine learning can offer and any of these other advanced technologies. To the extent that these elements provide a more vital bulwark for detecting and preventing cyber events. These technologies can also help create new and more dangerous attack vectors.
That’s why reports like Tiresias are so crucial to the future of cybersecurity, Semantic researchers say. “So far, cybersecurity has been about interactive security – this technology has been able to shift from a post-event approach to proactive action. Which is essential for the future,” said Pierre Antoine Verveer. Chief research engineer at Symantec and a member of Tiresias research team.
Also Read: Luca and alberto ages